Centralized collection and storage of traffic logs is one of the most important pieces of any enterprise security environment and it is crucial to have the information about the source (resource requester). In most cases this is as simple as installing an agent on the server and / or forwarding the log files to the log collector / SIEM etc. However, in some cases, it is not so straight forward.
Consider an Internet facing application that you have hosted in you Azure infrastructure. Just a quick refresher, an Azure Application Gateway:
- is an OSI Layer-7 load-balancer
- is capable of performing an SSL termination
- is a reverse proxy (like any standard load balancer)
- is capable of performing health checks of the backend servers (which host the actual application content) and thereby ensure that if one of the backend servers goes down, it automatically stops sending the traffic to this bad server and thereby save you from an outage
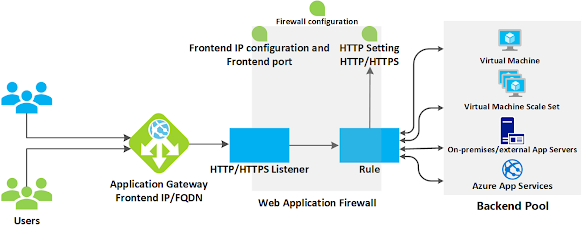
The following setup shows users enter the FQDN which resolves to the Frontend IP of the Application Gateway.
The HTTP/HTTPS listeners are the list of the URLs that you ask the Application Gateway to listen for.. For eg. if the listener configured is www.abc.com and if the user requests www.xyz.com (which is not configured as a listener on the Application Gateway, the traffic will be dropped there and then itself.
The rules dictate which backend pool (which contains our servers) the traffic will be forwarded to.
Now, here is the catch.
When the traffic leaves Application Gateway - AG (and heads towards one of the servers depending on the rule), the AG performs a "source NAT" on the traffic. The source IP of the packet leaving the Application Gateway is now changed to the AG's Backend IP address (this IP address is derived from the Backend Subnet that is configured for the AG).
This implies the servers (present in the backend pool) can NOT see the original IP address of the user who is accessing the application. All it sees is the backend IP of the Application Gateway. This definitely cannot be used for log and threat analysis, forensics etc. and defeats the entire purpose of doing a log collection.
However, Azure has a workaround for this.. Azure Application Gateway, while serving as the first termination point of the traffic, before changing the source IP to its backend IP, copies the original user IP address to X-Forwarded-For (acr. as XFF) header.
All the current servers and most of the older servers have the ability to read these XFF headers and forward them to the remote log collection server.
This way, the original user IP address is still retained with our logs and all the relevant traffic from the particular user IP address can be retrieved and analyzed.


Thanks, What exact header value to be enter for X-Forwarded-For to remains Client IP as source for backend pool.
ReplyDelete